Planning with Precision
Planning with Precision
Clarity That Translates Strategy Into Outcomes
Surface clarity from obscurity
Prioritize what truly matters
Get primed for success
Overperform without overcommitting
Move with intention
A strategy without execution is a wish. Achieve your project’s success with practical roadmaps that eliminate wasteful effort, guiding every step of the planning process to align your technological needs with your budget and timelines.
There’s guesswork. And then there’s NRI IT Advisory & Consulting.
Strategic experience, frontline fluency
Roadmaps made for action
Security embedded at the foundation
Clarity That Translates Strategy Into Outcomes
Surface clarity from obscurity
Prioritize what truly matters
Get primed for success
Overperform without overcommitting
Move with intention
There’s guesswork. And then there’s NRI IT Advisory & Consulting.
Strategic experience, frontline fluency
Roadmaps made for action
Security embedded at the foundation
Strategizing as a Business Analyst in the World of AI
Strategy That Sees Around Corners
Business Advisory & Planning
Technology Strategy & Consulting
Security Assessment & Risk Mitigation
Relevant News & Insights

The Anatomy of a Successful Tabletop Exercise
Congratulations! You’ve successfully pitched the value of a Tabletop Exercise (TTX) and secured executive buy-in. Now the real work begins– designing an exercise that is more than just a theoretical […]

How to Sell a Tabletop Exercise to Your Board: The Value Proposition Talking Points
The dreaded email: Your proposal for a comprehensive Tabletop Exercise (TTX) has been sent to the executive leadership. Weeks pass. The final answer? “It’s expensive” or “We don’t have time […]

What is a Tabletop Exercise? The Crisis Rehearsal Your Business Needs
Imagine it’s 2:00 AM on a Tuesday. Your Chief Information Security Officer (CISO) gets a notification: a critical database has been encrypted. By 8:00AM, the phones are ringing off the […]

Zero Trust in 2026: Protecting Field Devices, Smart Meters, and Legacy Systems
Identity weaknesses are a prime target in today’s distributed, hybrid environments. Thus, Zero Trust is non-negotiable Today’s power plants, factories, and utility grids look very different from they did a […]

The IT Trends That Defined 2025 and What Comes Next in 2026
As 2025 comes to a close, one thing is clear. Technology strategy is no longer about keeping pace. It is about building the foundation for what comes next. Across industries, […]
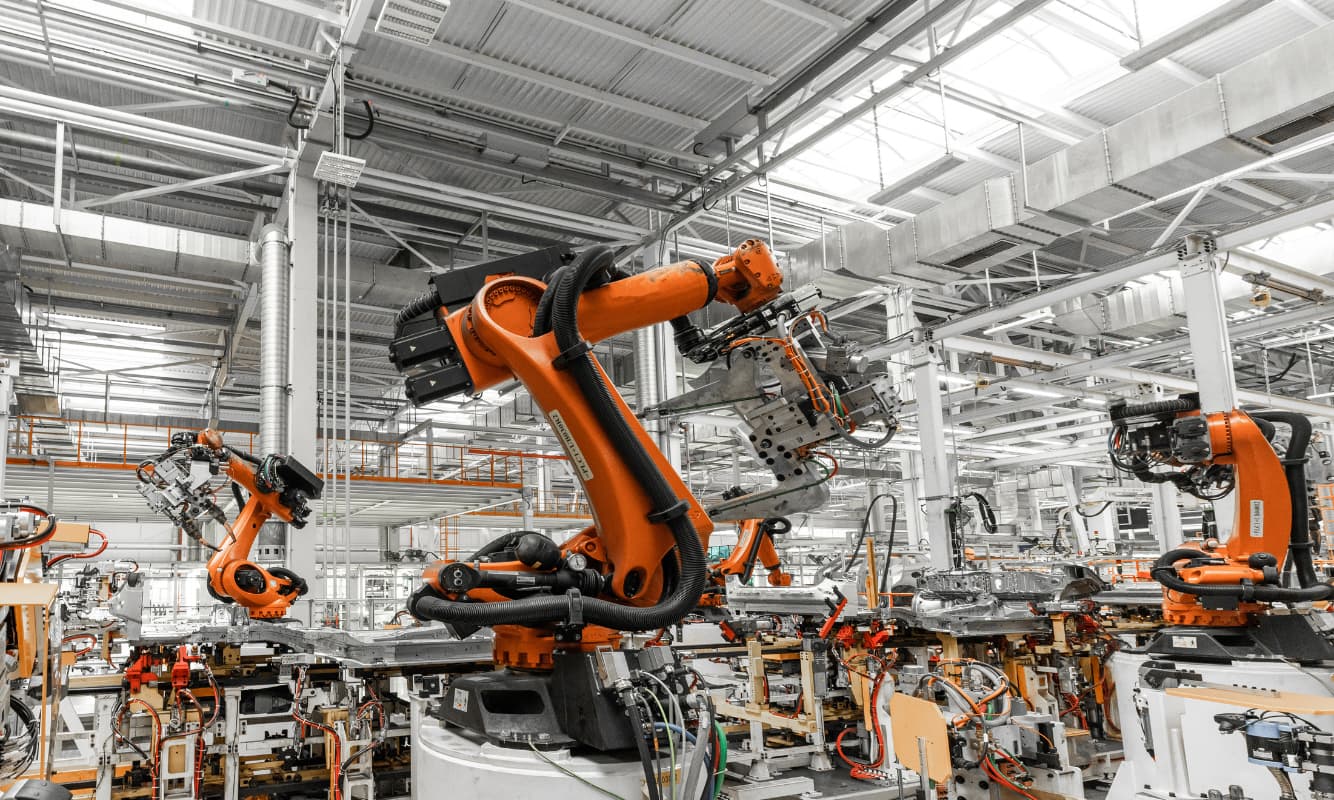
Emerging Cyber Threats Targeting IIoT and How Manufacturers Can Stay Ahead
Unlock the value of connected operations without compromises. The Industrial Internet of Things (IIoT) has become the driving force behind modern manufacturing. Sensors, autonomous robots, cloud gateways, and other connected […]